You know that sinking feeling when a platform you actually use may have been breached? This is one of those moments.
The notorious extortion group ShinyHunters claims to have publicly dumped 1.4 million Udemy user records after the company reportedly did not meet an April 27 ransom deadline. The dataset has been indexed by Have I Been Pwned, which adds credibility to the claim. If confirmed, the data contains highly sensitive personally identifiable information (PII) affecting both students and instructors.
However – and this is important – Udemy has not yet issued an official statement. The full scope, method of compromise, and authenticity of every data point remain unverified. Treat the following analysis as a report on claims made by a known threat actor, with independent corroboration from HIBP and multiple security news outlets.

The Alleged Breach: A Timeline
According to ShinyHunters' posts and subsequent coverage by Economic Times and eSecurity Planet, the timeline unfolded as follows:
While HIBP’s inclusion strongly suggests the data is legitimate, independent verification of every record is ongoing. Udemy has not confirmed or denied the breach as of publication.
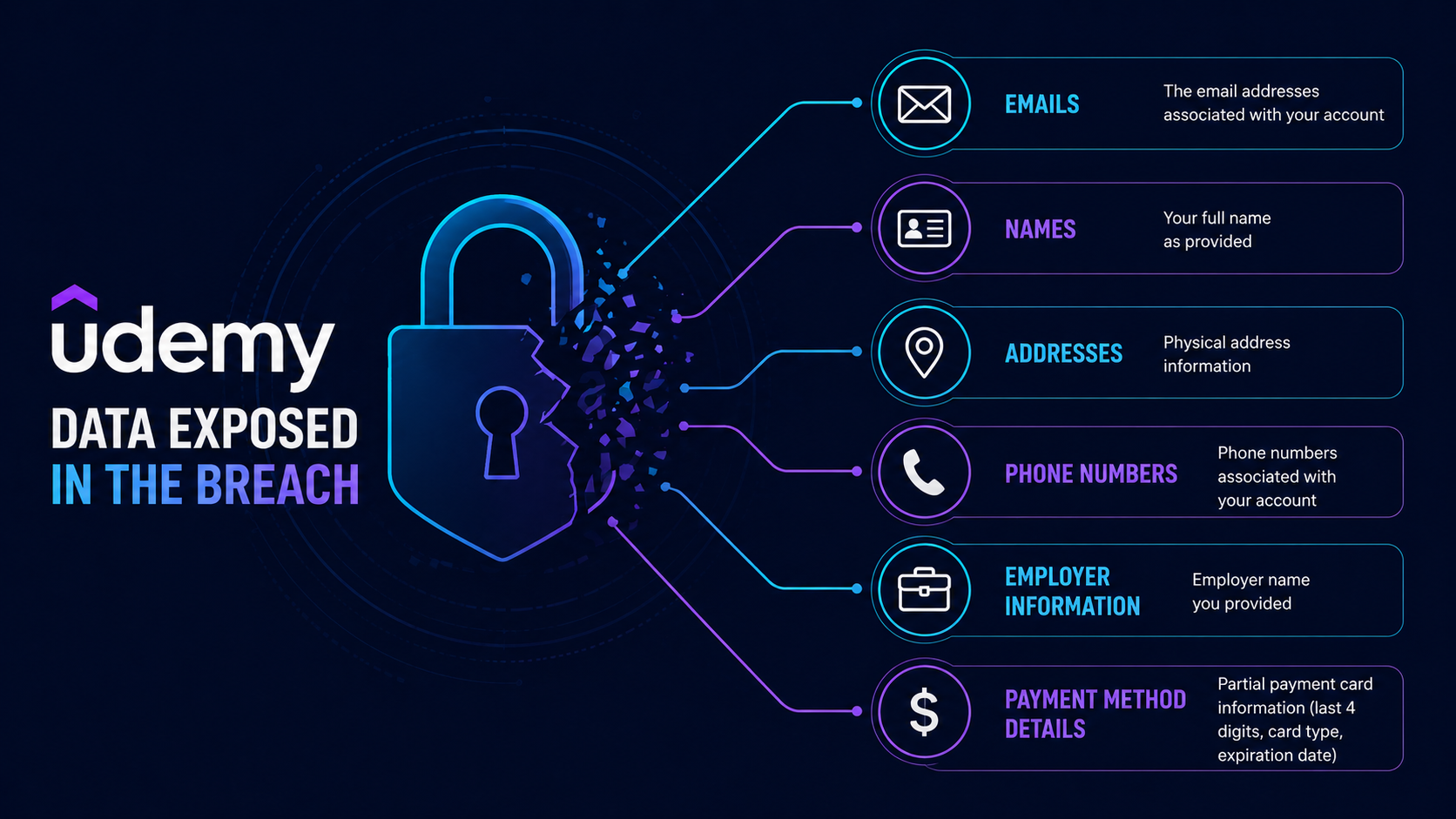
What Data Is Allegedly Exposed
According to Have I Been Pwned and reporting by cybersecurity news outlets, the dumped dataset is said to contain:
- Email addresses
- Full names
- Phone numbers
- Physical addresses
- Employer information (company name, work email domain)
- Job titles
- Payment method information – including PayPal email addresses, bank transfer reference data, and check details (primarily for instructors)
Of the 1.4 million email addresses reportedly in the leak, 56% were already present in HIBP’s database – suggesting widespread credential reuse across platforms.
Critical nuance – what “exposed payment data” does and doesn’t mean:
The leaked data reportedly contains instructor payout details such as PayPal email addresses and bank transfer identifiers. This does not give attackers direct access to those financial accounts. However, it does provide threat actors with valuable information to launch targeted phishing campaigns, credential‑harvesting attacks, and social engineering attempts against instructors. Attackers could, for example, impersonate Udemy support and ask for login credentials or use the PayPal email address to send fake payment alerts.
Direct financial theft would require much more than these identifiers – but the risk of secondary scams is significant and real.
Who Is ShinyHunters? (A Short History)
ShinyHunters is a prolific data extortion group known for stealing large databases and threatening to leak them unless a ransom is paid – without using encryption.
- 2020–2022: Sold over 200 million stolen user records from Tokopedia, Unacademy, and other platforms.
- June 2024: Claimed responsibility for breaches at Ticketmaster (up to 560 million users) and Santander.
- 2025 – Salesforce vishing campaign: Google Threat Intelligence linked UNC6040 (believed to be ShinyHunters) to voice phishing attacks that tricked employees into authorising malicious connected apps, leading to data theft at Google, Adidas, LVMH, Cisco, and others.
- March 2026: Claimed to have compromised Salesforce, Snowflake, Okta, and other major vendors.
- April 2026: Before Udemy, the group claimed responsibility for leaking 78.6 million Rockstar Games analytics records and 1.7 million Hallmark customer records.
Despite arrests of alleged BreachForums administrators in June 2025, the group continues to operate.
ShinyHunters typically gains initial access through vishing that compromises an employee’s SSO, crawls for valuable data using automated export tools, and then issues a “pay or leak” ultimatum. They do not encrypt files. Prevention and rapid detection are your only defences.
Uncertainty & Open Questions
Because Udemy has not issued an official statement and the full dataset is not publicly verifiable by independent researchers, several important questions remain unanswered:
- Was Udemy directly breached, or did the data originate from a third‑party partner? ShinyHunters has previously gained access via compromised contractor accounts (e.g., the 2025 Salesforce campaign).
- Are all 1.4 million records current and accurate? Some entries may be outdated or scraped from other sources.
- Has Udemy reset affected users’ passwords? No official communication has been observed.
- Will Udemy offer fraud protection or credit monitoring? Unknown.
ThreatAft will update this article as more information becomes available.
What You Should Do – Regardless of Uncertainty
Given the HIBP indexing and the group’s track record, assume the worst and take protective steps now.
🔴 For Udemy Users
- Check Have I Been Pwned: Visit HIBP and search your email.
- Reset your Udemy password immediately – use a strong, unique password. Do not reuse it elsewhere.
- Enable two‑factor authentication (2FA) on Udemy if available.
- Review your account for unauthorised course enrollments or changes.
🟠 For Udemy Instructors
- Change your PayPal password (do not reuse the Udemy password).
- Monitor linked financial accounts for suspicious activity – but remember, attackers cannot directly withdraw funds with just an email address.
- Be extremely wary of phishing emails claiming to be from Udemy “payment support” or “verification required.”
- Contact your bank to add fraud alerts if you believe your bank account details were exposed.
🟡 General Best Practices
- Expect targeted phishing campaigns using your name, employer, and Udemy association.
- Never click links in unsolicited messages – navigate directly to Udemy.
- Use a password manager to generate and store unique credentials.
- Monitor your credit reports for signs of identity theft.
External Resources
- Have I Been Pwned – Udemy breach check
- CISA Ransomware and Data Extortion Guide
- Economic Times – ShinyHunters claims Udemy data breach
- eSecurity Planet – Full analysis
Related Reading on ThreatAft
- UNC6692: Email Bombing + Teams Helpdesk Impersonation
- Weaponization of AI: Autonomous Cyber Attacks
- ZionSiphon: OT Malware Targeting Water Systems
The Bottom Line
ShinyHunters has a long history of following through on extortion threats. While Udemy has not confirmed the breach, the inclusion of the dataset in Have I Been Pwned is a strong signal that user data has indeed been exposed.
But don’t panic – act. Change your password. Turn on 2FA. Stay vigilant against phishing. And stop reusing passwords, because even if this breach is smaller than claimed, your credentials are now in the hands of a motivated extortion group.
For organisations, this incident reinforces that identity is the new perimeter. Strengthen MFA, audit third‑party access, and train employees to recognise voice phishing.
Stay skeptical. Stay secure. And check HIBP today.
Written by: ThreatAft Security Team – Specialising in data breach analysis and threat actor profiling.