You know that sinking feeling when you realise the very tool meant to protect you has become a weapon against you? That's the reality for Windows administrators this week.
Three Microsoft Defender zero-day vulnerabilities are being actively exploited in the wild. Attackers are using them to gain SYSTEM-level privileges and block Defender definition updates – essentially turning off the lights while they ransack the house. Only one has been patched. Two remain wide open.
This isn't theoretical. Real attacks are happening right now. Let's break down what you need to know.

What's Happening?
Beginning in early April 2026, a security researcher operating under the aliases Chaotic Eclipse and Nightmare Eclipse began publishing proof-of-concept exploit code for three previously unknown vulnerabilities in Microsoft Defender. The release was reportedly a protest against Microsoft's handling of the disclosure process.
By April 10, attackers had already weaponised the first exploit. By April 16, all three were being used in real-world intrusions.
According to Huntress Labs security researchers, the exploitation involves hands-on-keyboard activity by threat actors – not automated malware – indicating targeted, deliberate attacks rather than opportunistic campaigns.
In one confirmed incident, attackers gained initial access through a compromised SSL VPN account – likely exploiting the critical Windows IKE RCE (CVE-2026-33824) we covered earlier. After breaching the VPN, they deployed the three exploits in sequence to escalate privileges and degrade endpoint defences.
The Three Vulnerabilities
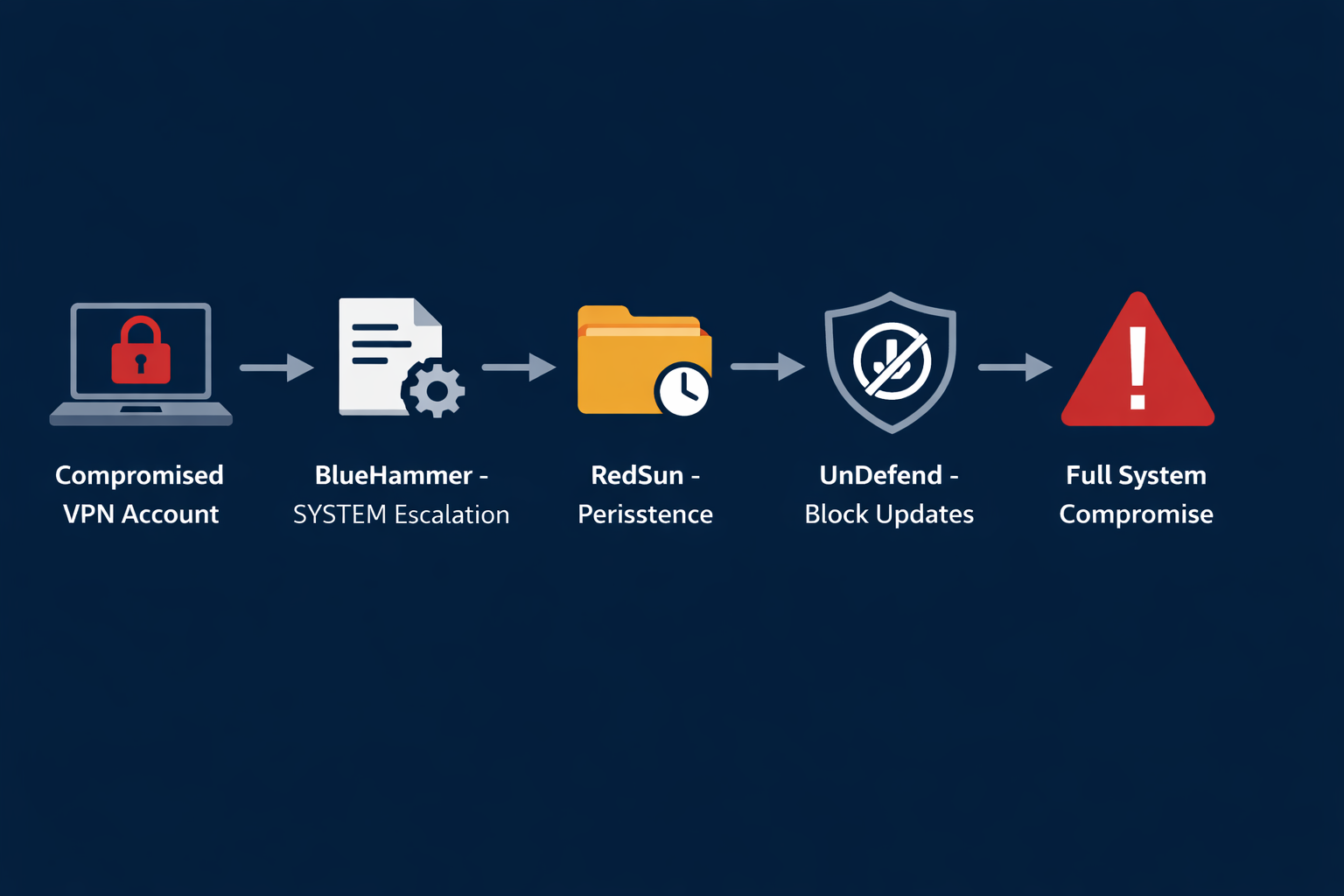
🔨 BlueHammer (CVE-2026-33825) – PATCHED
BlueHammer is a local privilege escalation (LPE) vulnerability in Microsoft Defender's signature update mechanism. It abuses a time‑of‑check to time‑of‑use (TOCTOU) race condition, chained with path confusion, to achieve SYSTEM‑level privileges.
The vulnerability allows a low‑privileged local user to escalate privileges to NT AUTHORITY\SYSTEM – the highest privilege level on Windows. It does not rely on memory corruption or kernel exploitation. Instead, it abuses a sequence of legitimate Windows features during Defender's signature update process, resulting in temporary access to normally locked registry hives, including the Security Account Manager (SAM), which stores local credential hashes.
CVSS Score: 7.8 (Important)
Patch Status: ✅ Fixed in Defender Antimalware Platform version 4.18.26050.3011 (released April 14, 2026)
Update method: Automatic through Windows Security
First observed exploitation: April 10, 2026
Microsoft has assigned this vulnerability the official CVE identifier CVE-2026-33825. The first public proof-of-concept appeared on GitHub on April 3, 2026, after the researcher claimed that a disclosure attempt with the Microsoft Security Response Center (MSRC) went nowhere.
☀️ RedSun – UNPATCHED
RedSun is a second local privilege escalation flaw that remains unpatched as of April 18, 2026. It exploits how Microsoft Defender handles cloud‑tagged files by combining legitimate Windows features, including the Cloud Files API, opportunistic file locks, Volume Shadow Copy coordination, and directory junctions.
When Windows Defender detects a file with a cloud tag, the antivirus rewrites the file to its original location. The researcher explained: "The PoC abuses this behaviour to overwrite system files and gain administrative privileges."
This behaviour allows Defender, running with SYSTEM privileges, to overwrite protected system files and execute attacker‑controlled code on fully patched systems.
CVSS Score: Not yet assigned
Patch Status: ❌ No patch available as of April 18, 2026
Affected Systems: Windows 10, Windows 11, Windows Server 2019 and later (with Windows Defender enabled)
First observed exploitation: April 16, 2026
RedSun does not currently have an assigned CVE identifier. Microsoft has confirmed it is investigating the remaining vulnerabilities but has not announced a patch timeline.
🚫 UnDefend – UNPATCHED
UnDefend is the third flaw, targeting Microsoft Defender's update mechanism. It allows a standard, unprivileged local user to block or disrupt Defender definition updates, effectively preventing the antivirus from receiving new malware signatures.
Over time, this reduces malware detection coverage, leaving systems increasingly vulnerable to newer threats. In some configurations, it can even disable Defender entirely.
CVSS Score: Not yet assigned
Patch Status: ❌ No patch available as of April 18, 2026
First observed exploitation: April 16, 2026
Like RedSun, UnDefend lacks an official CVE identifier. The researcher published the PoC exploit on GitHub on April 16, and Huntress confirmed its use in the wild the same day.
Detection – Event IDs & IOCs
To hunt for potential exploitation of these zero‑days, focus on the following Windows Event Logs and indicators:
- Event ID 4672 (Special Logon): Indicates a successful logon with administrative privileges. Unexpected occurrences may signal privilege escalation via BlueHammer or RedSun.
- Event ID 2001, 2002, 2003 (Defender Update Failures): These events are logged when Defender cannot download or install signature updates. A sudden spike may indicate UnDefend activity.
- Unexpected processes in user folders: Look for executables named to mimic legitimate files (e.g., `svchost.exe`, `defender_update.exe`) inside `C:\Users\*\Pictures\` or `C:\Users\*\Downloads\`.
- Suspicious PowerShell commands: Enable module and script block logging. Hunt for invocations that manipulate Defender settings or attempt to overwrite system files.
Huntress observed the attacker dropping exploit files into user directories and running enumeration commands like `whoami /priv`, `cmdkey /list`, and `net group` before launching the exploits. These are strong indicators of hands‑on‑keyboard activity.
What You Need to Do Right Now
🔴 Immediate (Today)
- Verify BlueHammer patch status. Check that Defender Antimalware Platform version is 4.18.26050.3011 or later. This updates automatically via Windows Security, but confirm it has applied.
- Review VPN access logs. The confirmed incident involved a compromised SSL VPN account – likely via the Windows IKE RCE. Look for unusual login times, locations, or concurrent sessions.
- Check for suspicious processes. Look for unexpected executables in user folders (Pictures, Downloads) named to avoid detection.
🟠 This Week
- Hunt for RedSun and UnDefend IOCs. Use the Event IDs and indicators listed in the Detection section above.
- Limit local administrative privileges. Both RedSun and BlueHammer require local execution. Reducing local admin rights limits attack surface.
- Enable PowerShell logging. The exploits may be executed via PowerShell. Enable module logging, script block logging, and transcription.
- Implement network segmentation. Isolate critical systems from general-purpose endpoints. Lateral movement becomes harder when network segments are properly separated.
🟢 Long-Term
- Adopt Zero Trust principles. Assume compromise. Verify every access request, regardless of source.
- Deploy endpoint detection and response (EDR). Microsoft Defender alone isn't sufficient. Consider supplementary EDR solutions that can detect post-exploitation behaviour.
- Regularly test offline backups. If attackers gain SYSTEM access, they can deploy ransomware. Ensure backups are immutable and regularly tested.
- Subscribe to Microsoft security advisories. Don't rely on social media for patch notifications. Use official MSRC feeds.
External Resources
- Microsoft Security Response Center – CVE-2026-33825
- The Hacker News: Three Microsoft Defender Zero-Days Actively Exploited
- BleepingComputer: Recently leaked Windows zero-days now exploited in attacks
- Help Net Security: Researcher drops two more Microsoft Defender zero-days
- Field Effect: Three Microsoft Defender Zero-days Reported Exploited
Related Reading on ThreatAft
- Microsoft Patches Actively Exploited SharePoint Zero-Day – CVE-2026-32201
- Critical Windows IKE RCE (CVE-2026-33824): Patch Your VPN Servers Now
- ZionSiphon: The OT Malware That Could Poison Water Supplies
The Bottom Line
Three Microsoft Defender zero-days. Two still unpatched. Active exploitation confirmed. Attackers are using them right now – often after breaking in through unpatched VPNs like the IKE RCE we warned about earlier.
BlueHammer is fixed – verify your Defender version today. RedSun and UnDefend have no patch. Until Microsoft releases an update (likely an out‑of‑band emergency patch given the urgency), your best defence is hunting for IOCs, limiting local admin rights, and monitoring for unusual Defender behaviour.
Don't wait for the next Patch Tuesday. Attackers certainly aren't.
Go hunt. Then go have that coffee. You've earned it.
Written by: ThreatAft Security Team – Specialising in Windows security and threat intelligence.