You know that feeling when a security advisory lands in your inbox, and your stomach drops? This is one of those moments.
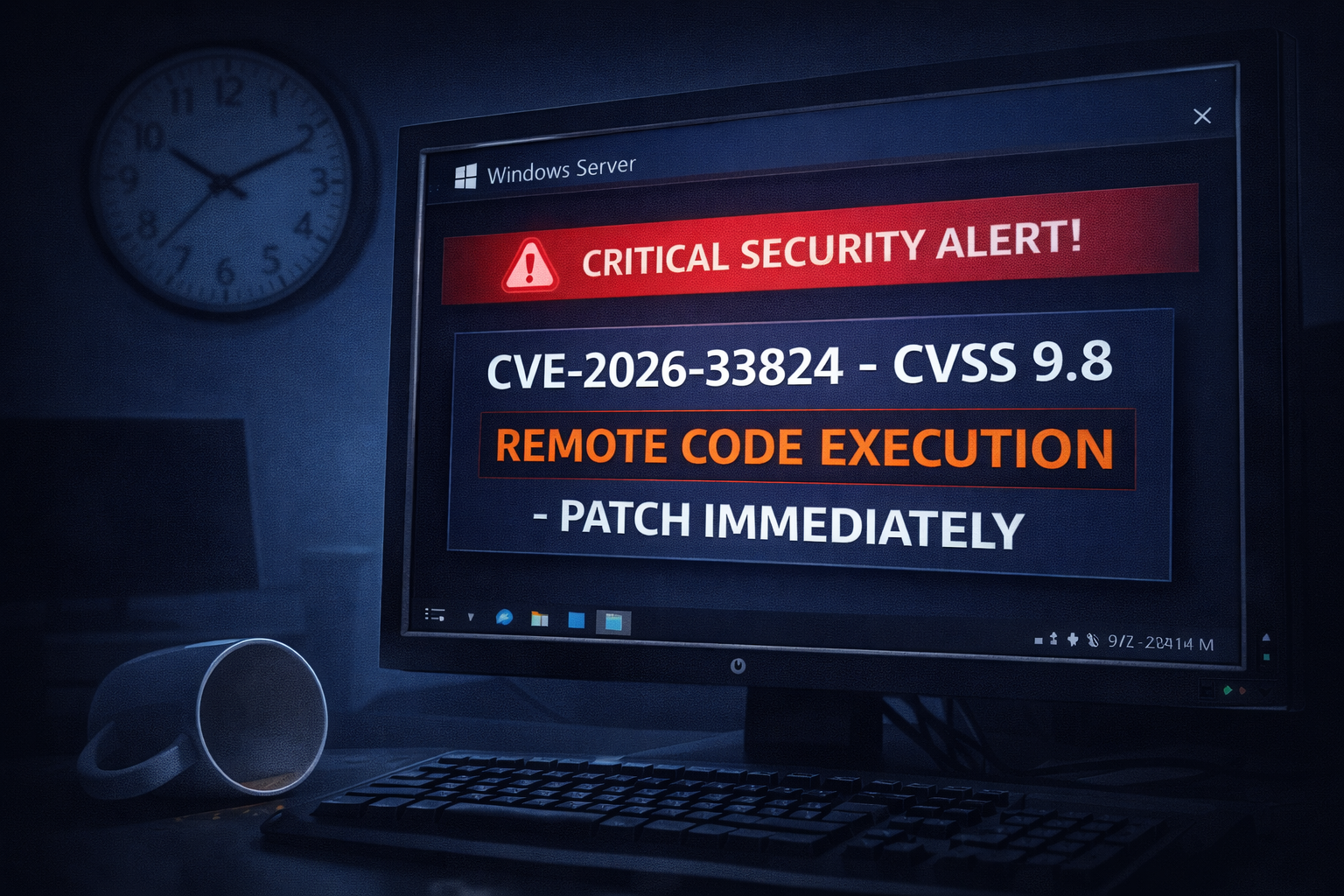
Microsoft's April 2026 Patch Tuesday fixed a critical remote code execution (RCE) vulnerability in the Windows Internet Key Exchange (IKE) service. Tracked as CVE-2026-33824, it carries a CVSS score of 9.8 – that's "drop everything and patch now" territory.
The kicker? An unauthenticated attacker can exploit this over the network without any user interaction. No phishing emails. No malicious attachments. Just a few carefully crafted network packets sent to your VPN server, and they're in.
What makes this so dangerous: The IKE service is core to Windows VPN functionality. If you run a Windows Server as a VPN gateway (SSTP, L2TP/IPsec, or IKEv2), your server is exposed to anyone who can reach it over the internet or your internal network. Attackers can send a specially crafted IKE packet that triggers a double‑free memory corruption, leading to remote code execution with SYSTEM privileges.
Once they're in, they can disable your firewall, steal VPN credentials, pivot to internal systems, or deploy ransomware. All before your Monday morning coffee.
Who is affected? The vulnerability impacts:
- Windows Server 2016, 2019, 2022, and 2025
- Windows 10 (versions 1607, 1809, 21H2, 22H2)
- Windows 11 (21H2, 22H2, 23H2, 24H2, 25H2, 26H2)
If your system has the IKE service enabled and is reachable via UDP port 500 and 4500, you're vulnerable. That's most VPN servers and some domain controllers that use IPsec.
Has it been exploited yet? As of April 15, 2026, Microsoft has not observed active exploitation. However, the vulnerability was discovered internally and disclosed responsibly. The German Federal Office for Information Security (BSI) issued a security warning on April 14, urging immediate patching. Given the CVSS score and the fact that a patch exists, exploit code is expected within days to weeks. Attackers reverse‑engineer patches for fun and profit.
What you need to do right now:
🔴 Immediate (today)
- Apply the April 2026 cumulative update via Windows Update or the Microsoft Update Catalog.
- Restart your server – the fix requires a reboot.
- Verify the update installed correctly: check for KB numbers specific to your OS version (e.g., KB5056783 for Server 2022).
🟠 If you cannot patch immediately
- Block inbound UDP ports 500 and 4500 on your firewall for untrusted networks.
- Disable IKEv2 VPN connections and switch to SSL VPN (SSTP) temporarily.
- Monitor Windows Event Logs for Event ID 20226 (IKE service crashes) – that could indicate scanning or exploitation attempts.
🟢 Long‑term
- Enable the Windows IKE service extended logging to capture attack patterns.
- Segment your VPN servers from critical internal systems.
- Subscribe to Microsoft's Security Update Guide RSS feed – don't rely on social media for patch news.
Wait – does this affect home users? Possibly. If you use Windows 10 or 11 with the built‑in VPN client or have the Routing and Remote Access Service (RRAS) enabled, you're vulnerable. Most home users don't have the IKE service exposed to the internet, but it's still worth running Windows Update tonight.
The bigger picture: This vulnerability is a reminder that VPN infrastructure is a prime target. In 2025, attackers exploited similar flaws in Palo Alto Networks and Cisco VPN appliances to breach thousands of organisations. Windows IKE is no different – it's a high‑value entry point.
Internal linking: For more on recent Patch Tuesday zero‑days, check out our article on actively exploited SharePoint spoofing (CVE-2026-32201). And if you're responsible for healthcare IT, read our breakdown of the ChipSoft ransomware attack that disrupted Dutch hospitals.
External references (trusted sources):
- Microsoft Security Response Center – CVE-2026-33824
- NVD entry with CVSS vector
- CISA KEV Catalog (not yet added, but monitor)
- German BSI security warning (14 April 2026)
The bottom line: CVE-2026-33824 is one of the most dangerous vulnerabilities patched this year. It's wormable, remotely exploitable, and requires no user interaction. If you run Windows VPN servers, treat this as an emergency.
Patch now. Test your backups. And maybe buy your sysadmin a coffee – they're going to need it.
Written by: Alex Rivera, ThreatAft Security Analyst (specialising in Windows infrastructure and network security).